Keeping a Shop Network Safe
Concerns about cyber security should not stop shops from installing machine-monitoring systems.
Many machining companies and job shops are interested in machine-monitoring systems. These systems connect machine tools and other manufacturing equipment to a network so data generated by the connected machines can be collected and analyzed by the monitoring software. Machine monitoring helps a shop keep tabs on production stats, job status, uptime and setup.
Most monitoring systems use internet technology for the shop network. This has current and potential users concerned because cyber security has become an urgent topic in discussions of the emerging Industrial Internet Things. Scenarios about the dangers of hackers, viruses, malware, data theft and other threats can be alarming.
We talked about this with Bill Bither, CEO and founder of MachineMetrics, a supplier of machine monitoring systems and manufacturing analytics in Northampton, Massachusetts. His company has installed machine-monitoring systems in numerous machine shops since its founding in 2014, with more than a thousand machines now being actively monitored. Mr. Bither’s experience with shop networking and networking security has given him insights into the risks and benefits of connecting machine tools to a network for monitoring purposes.
To start off, Mr. Bither explains that most threats would be posed by a hacker who is specifically targeting a company and its data. Fortunately, such attacks on machine shops are rare. “Unlocking the potential of your machine data can bring massive productivity gains, and this prospect certainly outweighs the risks,” he says.
He notes that there is a common misconception that networking machine tools means that they are immediately accessible on the public internet. “In truth, even the most basic network connected to the internet places a router in front of the internet connection, so any hacker from the outside would be unable to access the machines directly. However, this provision does not protect against vulnerabilities arising from unprotected software and sophisticated intrusions,” he says.
Mr. Bither identifies eight steps for protecting machines while they are being monitored. He cautions that these steps should be taken as a starting point for understanding network security. “What’s important is to note that these steps are manageable,” he says. “They should give shops considering machine-monitoring systems the confidence to move ahead, especially if they address network security with system providers.”
1. Change all default passwords on routers and managed switches.
You don’t want anyone on your network (a hacker or an employee) to be able to change your router’s settings. An unknowing employee or vendor could accidentally open up a security hole in this way. A hacker who manages to get on a network could do a lot of damage using default passwords.
When shops set up a network, a password is usually needed for the initial configuration of the routers and switches. Network vendors usually provide a default password (such as “admin”) that’s a convenience during the configuration process. This default password enables the installation technician or network administrator to establish settings for the routers and switches the network needs to connect to the internet or separate networks so data can be exchanged.
Once the network is configured and tested, the default passwords should be changed. At the same time, the shop needs to determine who will know the new password for changing network router settings or connections to a managed switch, as these control how connected devices will communicate with other devices on the network or interconnected networks. Normally, a network must have someone identified as the network administrator. This is usually someone with an IT background, most likely the person who participated in the network installation. However, in smaller shops, this role may be relegated to a shop manager or the shop owner (or even an administrative assistant in the front office). These individuals may not recognize the importance of changing passwords once the network is up and running.
Many smaller shops use the option of outsourcing network maintenance to a commercial IT vendor, who should be aware of password protection and can advise abouot maintaining it. In any case, leaving default passwords in place is risky because hackers have lists of common default passwords set by the manufacturer, so these passwords offer little or no protection.
2. Use the best available wireless encryption.
Never use a wireless network without encryption. Encryption simply means that the network protocol has provisions to scramble and unscramble messages as they are transmitted and received, respectively. However, older approaches to encryption such as WEP (wireless encryption protocol) are easy to hack. The newer alternative, WPA (Wi-Fi protected access), is difficult to hack. The latest generation of this protocol, WPA2, is even more resistant to hacking. Even so, with the right tools and enough time, WPA and WPA2 encryption can be hacked. That’s why a shop’s most sensitive information should not be accessible from a wireless connection.
Of course, most shops have basic Wi-Fi on the shop floor. This is suitable for checking email, browsing the web and so on. However, this Wi-Fi is not generally robust enough for machine monitoring. Real-time machine monitoring requires reliable connections to each machine. Shop environments typically are very “noisy.” Machines and equipment on the shop floor randomly emit electrical energy and radio waves at various frequencies. This noise can disrupt data transmissions being sent wirelessly. Even shops with networks using robust industrial Wi-Fi access points and repeaters can experience occasional brief dropouts of data. For this reason, a hard-wired network is always more reliable. For a hard-wired network, the protection of encryption rarely justifies the added complexity it entails.
When communicating remotely with a shop network via the internet, encryption is generally provided on a higher level. For example, when communicating with a system such as MachineMetrics, all data is encrypted through the secure web protocol HTTPS. Even if a remote user were on an unencrypted Wi-Fi or cellular connection, and an attacker was able to intercept every data packet, the sensitive data would be undecipherable.
3. Ensure all personal computers and servers on the network are up to date.
A shop network for machine monitoring is likely to include connections to a variety of PCs. These include desktops used in engineering, programming and management offices, as well as PCs that are part of the control systems on CNC machine tools (often referred to as PC front-ends) used for the operator interface. Any PC that hasn’t had security updates to its software is much more vulnerable to phishing emails and viruses when opening unknown email attachments or running suspicious downloaded applications.
Hackers often use large, pirated email lists to deliver messages with hidden viruses or attractive invitations to download applications that can secretly take control of the PC. These campaigns to make unauthorized use of PCs on a network can be launched without warning (and are often referred to as “zero-day exploits” because there are zero days for security software providers to take countermeasures). Unless this is a targeted attack, a hacked PC will likely be used as a spam email server, to find bank account details or to steal credit card numbers. If it is a targeted attack, the hacker could steal or modify sensitive company data that the compromised PC can access.
The network administrator is in the best position to make sure a shop’s networked PCs and servers have installed security updates to their operating systems. This should be done on a frequent, regularly scheduled basis. However, many machine controls with PC front-ends use older versions of the Windows operating system, for which security updates are no longer available. These PCs are often overlooked or cannot be updated when they do get the attention. For this reason, it is recommended to keep the factory network isolated from the company network.
Software providers, including providers of machine-monitoring software, often offer updates or upgrades to their products to introduce new features, add capability or fix bugs (code that does not function as intended). These upgrades may include improved security measures, so it is important to find out if these updates are urgently recommended. Cloud-based systems can implement these software updates and fixes for all licensed users at once, any time they are needed—one of the benefits of cloud-based applications.
4. Buy a hardware firewall and keep it updated.
A firewall is a method to control the inflow of data to a network or device on a network. The purpose of a firewall is to control this data traffic by inspecting packets (which include code that tells software what kind of data is being sent) or the data within the packet. The firewall then selectively allows or blocks this traffic from reaching its intended destination. Basically, a firewall operates as a checklist of rules. For example:
• If this is web traffic (TCP 80 and 443), let it pass.
• If this is email traffic (TCP 25), let it pass.
• If this file transfers traffic from the office server, let it pass.
• If this is anything else, block it.
For each data packet that comes in, the firewall will read the list of rules until it finds one that matches, and then take an action. The rules followed by a firewall are intended to protect computers against hacker attacks and other internet threats.
There are many inexpensive hardware firewalls available on the market (SonicWall, Linksys, Cisco, to name a few). Hardware firewalls are designed to protect the entire network, whereas most computers run their own software firewalls that apply rule sets for the same purpose. On a network, only one hardware firewall is required. It is usually installed in front of switches connected to the public internet.
The network administrator should make sure the firewall is properly configured to receive daily security updates, which usually requires an annual subscription to an online service. This service might include maintaining databases of dangerous IP address ranges or email spammers that can be blocked, for example.
5. Enforce strong passwords.
Make employees use strong passwords for all of their individual accounts. Make sure that any cloud service enforces the use of strong passwords over HTTPS, the secure version of the internet’s basic operating system. Using the names of one’s children, birthdays or other personal data makes a password easier to figure out, especially if the attack comes from an insider who may know these clues.
Strong passwords are more resistant to attempts to guess or crack them. Hackers use sophisticated algorithms that can be remarkably adept at decoding passwords that merely look complex because the creator substituted look-alike symbols for letters or followed some other strategy that only succeeded in making the password difficult to remember. Strings of eight or more random letter/number/symbol combinations are considered strong, but stringing together four or five random words can provide a similar level of security, even though they violate most conventional password complexity requirement rules. For reference, modern password generators consider strings of 16 or more random characters as very secure.
Two other tips about passwords are worth mentioning. Passwords should be changed periodically. If a user name and password have been compromised and are on a list available to hackers, the new password restores protection. Even more important, different passwords should be used for every site or account. This limits the damage a hacker can cause by accessing multiple data sources with the same stolen codes.
Finally, two-factor “authentification” is becoming more popular and should be noted. This method requires an additional entry that involves a physical device such as a USB memory stick or an app for generating a new key code that is reset every 30 seconds, during which time the key code must be used before its validity expires. Even if someone knows your password, it is not enough for that person to access your data because of the extra layer of security provided by the added factor.
6. Physically secure your facility.
Being on site (inside the shop, that is) makes a hacker attack much easier. Keep doors locked, install a security alarm system, or take other precautions to stop intruders from accessing your physical network. Of course, limiting access through entry ways by requiring a key card or entry code is a security measure that goes beyond protecting computers. However, many shops forget about loading docks, delivery bays, roof hatches and rarely used side doors as points of entry.
A more complex and challenging issue may be “securing” shop personnel. Trustworthy employees who take seriously all forms of shop security and safety are a vital defense against hackers and intruders.
7. Put your CNC or other sensitive machines on a VLAN.
A VLAN (virtual local area network) is an isolated network managed by a switch. This switch is set in the network software to determine which connected machines or devices can communicate. Once this switch is set, access to that network is limited. Because the switch operates in software, the physical cabling does not have to be altered to reconfigure the VLAN. You can lock down your equipment on a VLAN in a way that is separate from your primary network. One key benefit is that this separation prevents access to programmable logic controllers that run many machine tool subsystems.
These controllers are often overlooked by IT, so the software is not updated frequently. Many PLCs run a proprietary operating system that is relatively simple but efficient because it was developed to mimic the basic ladder logic used for wiring electromechanical circuits. This software is not very susceptible to viruses. However, many machine tool builders run their own operating system alongside their PLCs. This operating system is likely to be a version of Windows or Embedded Windows. This software, especially if it is running an older version of Windows, is more susceptible to viruses and should never have open access to the internet.
PLCs are unlikely targets of hackers because most hacker groups are generally unfamiliar with them. However, a targeted attack conceivably could be intended to disrupt operations on machine tools used in critical applications such defense or aerospace work. A PLC might serve as a weak spot for disabling a machine or causing it to produce out-of-spec parts without detection.
A factory VLAN should have no access to the public internet. A managed switch (available for around $500) will give a shop a very secure VLAN.
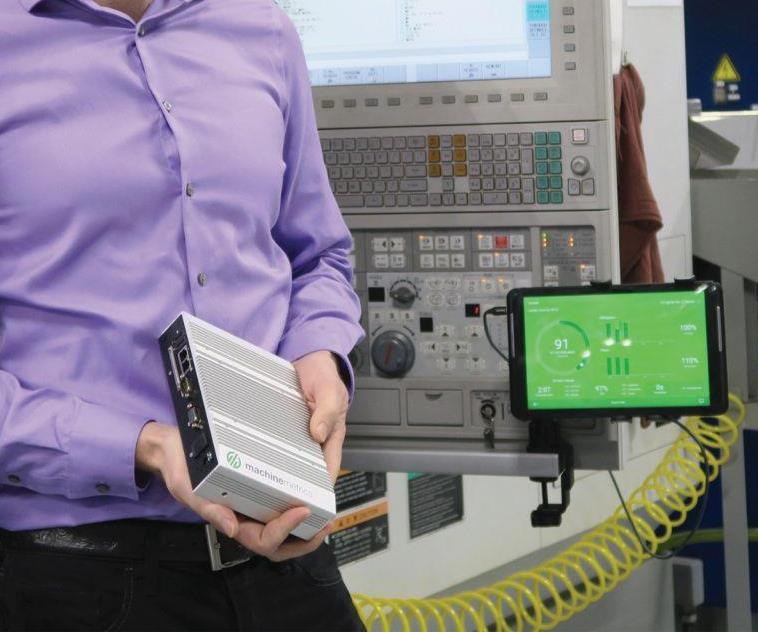
8. Manage connections to/from machines with a gateway.
If the machine network is separate from the employee network, how does a machine-monitoring service have real-time access to machine data? This is achieved through a gateway, with two network interfaces, that acts just like a managed switch. One network interface communicates with the locked-down machines’ VLAN. The other network interface communicates only with the machine-monitoring system. This protects the machines from communicating, even indirectly, with anything but the monitoring system.
For example, as a service to customers, MachineMetrics uses an industrial PC as a gateway. It is designed with two network interfaces—one that connects to the machine or machine network, and the other that connects to the public internet, or internal IT network. This product runs the on-premises gateway software that collects data from all machines via the MTConnect standard, encrypts that data and streams it to the cloud.
Typically, an installation requires a single gateway per location. A switch behind the gateway enables it to network all of the machines to be monitored. Should a shop want to isolate the machines from one another, the gateway should interface with a managed switch, whereby each data port represents its own VLAN or subnet. Otherwise a simple industrial unmanaged switch will suffice, and is recommended for ease of use and low cost.
Final Comment
Mr. Bither offered this concluding advice about networking machine tools to a monitoring system: “Proper networking is an engineering effort. You need someone that understands all of these concepts at a very deep level and takes responsibility for making sure it’s done properly.”
Related Content
Wireless Couplers Work Wonders for Workholding
Possibilities range from individual control of chuck jaws and tombstone fixtures to more reliable robots.
Read MoreSwiss-Type Control Uses CNC Data to Improve Efficiency
Advanced controls for Swiss-type CNC lathes uses machine data to prevent tool collisions, saving setup time and scrap costs.
Read MoreCan Connecting ERP to Machine Tool Monitoring Address the Workforce Challenge?
It can if RFID tags are added. Here is how this startup sees a local Internet of Things aiding CNC machine shops.
Read MoreShop Quotes Smarter, Works Harder with Machine Monitoring
Temco first installed MT-LINKi to optimize quoting. Now, the software helps the shop optimize its machines — and machine purchases.
Read MoreRead Next
3 Mistakes That Cause CNC Programs to Fail
Despite enhancements to manufacturing technology, there are still issues today that can cause programs to fail. These failures can cause lost time, scrapped parts, damaged machines and even injured operators.
Read MoreThe Cut Scene: The Finer Details of Large-Format Machining
Small details and features can have an outsized impact on large parts, such as Barbco’s collapsible utility drill head.
Read More










.png;maxWidth=300;quality=90)